Sunday, October 5, 2014
(Warning, wall of text!)
So we had this laser which probably not only had more interlocks than a nuclear reactor, but also actively prevented us from defeating those interlocks. What we wanted in the end was to be able to dial in a diode current, and have the diode driver run the diodes at that current. We also needed the crystal temperatures, water temperatures, and Q-switch settings to automatically adjust themselves according to the user current setting.
From the service information AMS had leaked on their website (the AMS Technical Services site is riddled with holes), we knew the following:
XPS but you get the idea
Knowing this, we had several approaches to turning on the laser.
(1) had the advantage of being guaranteed to work; however, it meant we would lose the self-protection that the stock Laserscope controller provided, and we figured that having things like underflow and overtemp were good. (2) was also known to work, and was pretty much a standard power analysis attack; unfortunately, neither of us had much experience in such techniques. (2) would have also given us a completely turn-key way to turn on the laser, one that did not involve any extra hardware.
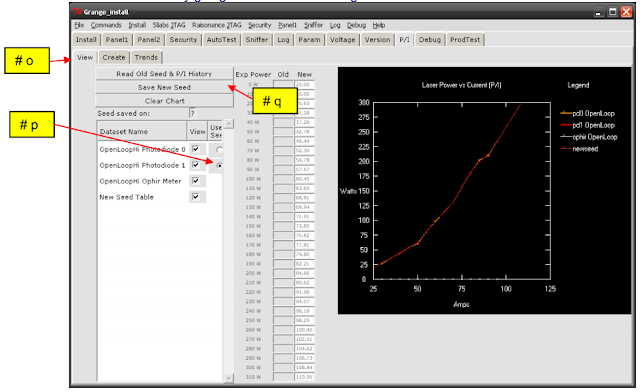
We decided to go with #3 because we had access to a borrowed CAN transceiver, and we figured it was a good middle ground between keeping enough of the internal firmware to protect the laser, while allowing us to hopefully build a custom user interface that did not look like a medical interface (as cute as the touchscreen was, being able to monitor critical laser parameters and set power in something other than 10W increments would have been real useful!)